Internet governance is often discussed through process.
Meetings are held.
Policies are proposed.
Consensus is tested.
Records are updated.
Procedures are followed.
These processes matter. A global network cannot function without coordination, documentation, and trust.
But process was never meant to become more important than the network itself.
The Internet’s deepest legitimacy has always come from operation. Networks connect. Packets move. Services run. Users depend on the infrastructure. Businesses build real systems around addresses, routes, records, and connectivity.
That is why Running-Code Betrayal matters.
Running-Code Betrayal describes the moment when governance process, institutional procedure, or policy interpretation begins to place live infrastructure at risk, even though that process was originally justified by the need to make the Internet work better.
For Larus.Foundation, this is not a slogan. It is a stewardship principle.
Internet number resource governance should protect operational continuity. It should not allow administrative process to become detached from the networks that are already running.
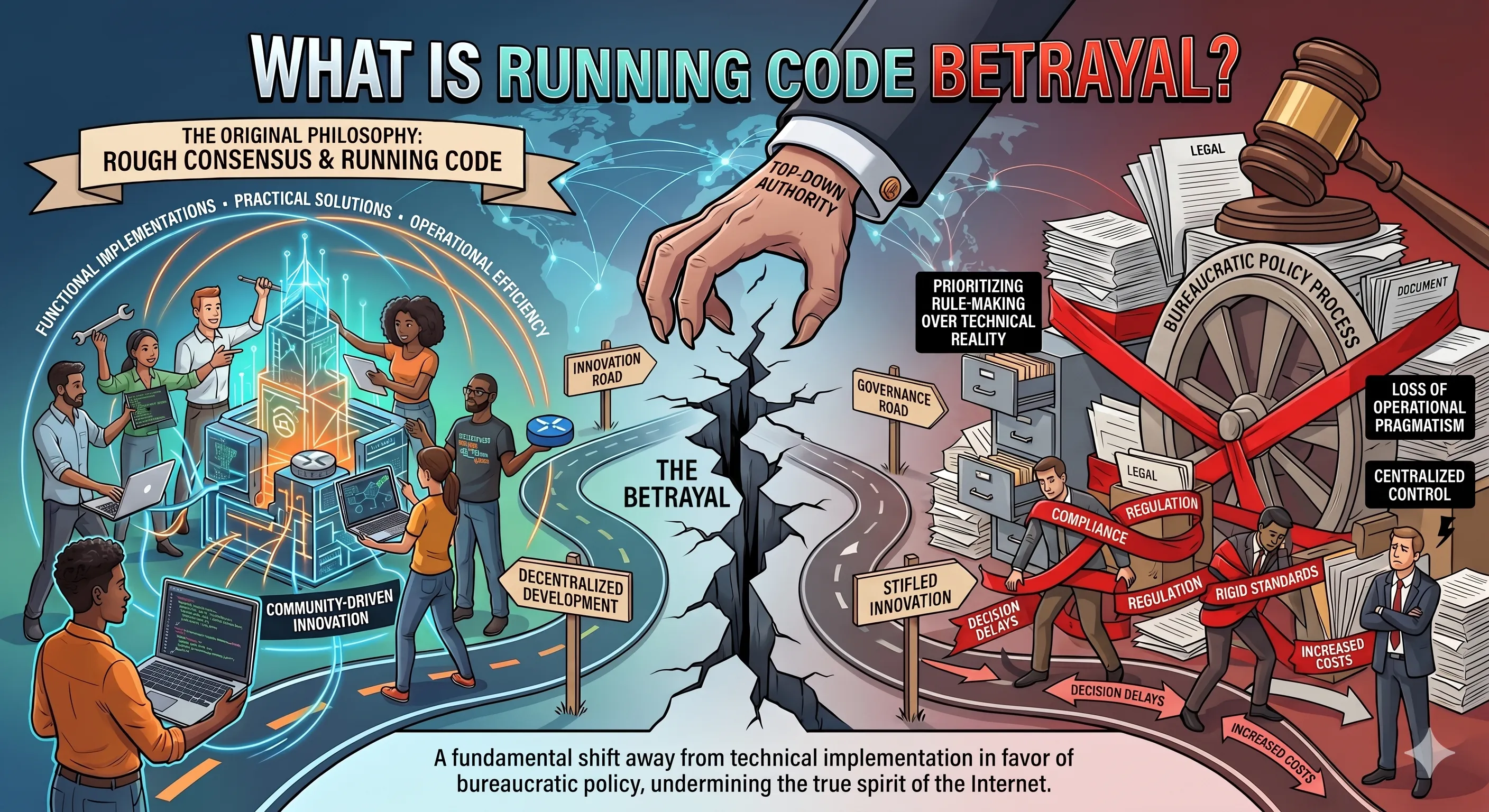
What Is Running-Code Betrayal?
Running-Code Betrayal occurs when a governance process uses the language of technical coordination while placing already-running infrastructure under pressure.
The phrase comes from the Internet engineering tradition of “rough consensus and running code.” That tradition did not mean that a room, committee, or process could claim authority over live networks simply because procedure was followed. It meant that technical judgment should remain grounded in operational reality.
In other words, process was supposed to serve the network.
Running-Code Betrayal happens when that order is reversed.
A process may be formally correct.
A meeting may be properly scheduled.
A policy may be debated.
A decision may be documented.
But if the result puts live networks, users, customers, or operational continuity at unnecessary risk, then the process has failed its deeper purpose.
A process justified in the name of operational reality cannot keep its legitimacy once it is used against operational reality.
Internet governance earns trust when it protects running systems.
It loses trust when it governs against them.
Why Running Networks Must Come First
A running network is not an abstract policy object.
It may support:
- websites
- cloud services
- telecom networks
- VPN platforms
- email systems
- healthcare systems
- banking infrastructure
- logistics platforms
- security tools
- government services
- small business operations
- customer-facing applications
When an IP resource is already in production, many dependencies may sit behind it.
Customers may have whitelisted the address.
Applications may depend on it.
DNS records may point to it.
Firewalls may trust it.
Routing policies may rely on it.
Email reputation may be attached to it.
Commercial contracts may assume continuity.
That is why running networks must come first.
This does not mean live infrastructure can never be governed, reviewed, transferred, corrected, or questioned. It means that any governance action affecting running infrastructure must be proportionate, evidence-based, careful, and aware of downstream consequences.
A policy process that ignores operational dependency is incomplete.
A registry decision that treats a live network as a static database entry is incomplete.
A governance model that speaks about community interest while overlooking actual users, customers, and operators is incomplete.
Operational continuity is not a side issue.
It is the reason the governance layer exists.
The Difference Between Coordination and Control
Coordination is necessary.
Internet number resources require uniqueness. Without coordination, different networks could claim the same address space, routing could become confused, and global interoperability would weaken.
A coordination layer can support:
- accurate records
- resource uniqueness
- transfer traceability
- routing confidence
- contact accountability
- abuse handling
- operational stability
But coordination is not the same as control.
Coordination helps the network remain legible.
Control can determine whether a network remains usable.
The difference matters.
A narrow coordination function is legitimate when it protects uniqueness and continuity. But when coordination expands into broad discretion over live resources, businesses and operators may face uncertainty over who truly controls the conditions of use.
Heng.lu doctrine repeatedly draws this line: record-keeping is not sovereignty, and administration is not title. The related source argues that once coordination is inflated into broader political or institutional entitlement, the registry function risks becoming something it was not designed to be.
For Larus.Foundation, this distinction is essential.
A healthy Internet resource system should coordinate the network without placing unnecessary discretionary pressure on the operators who keep it running.
Also Read: Is the RIR Model Sustainable in the Long Term?
Also Read: Mandate Laundering and Internet Resource Stewardship
Why Policy Process Can Become Operational Risk
Policy process can become operational risk when it moves faster than the affected network can safely absorb.
This can happen in several ways.
A rule may be interpreted broadly after resources are already deployed.
A documentation requirement may change after services are already live.
A transfer process may delay expansion.
A registry decision may create uncertainty around recognition.
A routing record may be questioned without a clear continuity path.
A compliance process may require evidence that smaller operators struggle to produce quickly.
A provider or registry framework may shift responsibility downward while preserving control above.
None of these issues automatically means wrongdoing. Governance systems often face difficult trade-offs.
But responsible stewardship must ask:
- Who is affected?
- What infrastructure is already running?
- What customers depend on it?
- What alternatives exist?
- What is the least disruptive path?
- What evidence supports the action?
- What remedy exists if the action is wrong?
- Who carries the operational consequence?
If these questions are ignored, process itself can become a risk layer.
That is how Running-Code Betrayal begins.
Not necessarily through dramatic failure, but through a slow reversal: the operational network becomes subordinate to the administrative process that was supposed to serve it.
Internet Number Resources Are Live Infrastructure
IPv4 addresses, IPv6 addresses, and Autonomous System Numbers are often described as records or resources.
That description is technically useful, but it can understate the real-world dependency behind them.
Internet number resources are embedded in live infrastructure.
A single IPv4 block may support hosting customers, SaaS systems, enterprise access, VPN platforms, telecom services, security tools, or cloud workloads.
An ASN may support routing relationships, upstream connectivity, traffic engineering, and operational independence.
A registry record may support transferability, route legitimacy, contact accuracy, and trust between operators.
This means that number resources cannot be treated only as administrative entries.
They are part of the operational environment of the Internet.
When governance touches these resources, it touches the systems built on top of them.
That is why Larus.Foundation frames Internet resource stewardship around continuity, accountability, and operational realism.
The question is not only:
“Was the process followed?”
The stronger question is:
“Did the process protect the network that people actually use?”
The E-E-A-T Problem: Governance Must Be Explainable
Google E-E-A-T is usually discussed in SEO terms: experience, expertise, authoritativeness, and trustworthiness.
But the same idea applies to Internet governance.
A trustworthy governance model must be explainable.
Operators should be able to understand:
- what rule applies
- who applies it
- why it applies
- what evidence is required
- what process exists for correction
- what continuity protections are available
- what remedy exists if a decision creates harm
If governance cannot explain itself clearly, trust weakens.
If governance relies on vague language, operators become uncertain.
If operators become uncertain, they plan defensively.
If they plan defensively, the system becomes less efficient, less trusted, and more fragmented.
Responsible Internet resource stewardship should be transparent, specific, source-aware, legally careful, and operationally useful.
It should avoid exaggeration.
It should avoid unsupported accusations.
It should avoid treating every procedural disagreement as misconduct.
But it should also avoid pretending that process is automatically legitimate just because it is process.
Trust requires more than procedure.
It requires clarity, accountability, and respect for running infrastructure.
How Running-Code Betrayal Affects Businesses and Users
Running-Code Betrayal may sound like an internal governance issue, but its effects can reach businesses and users.
For businesses, it may appear as:
- delayed deployment
- uncertain IPv4 transfer
- weaker routing confidence
- emergency migration
- lost customer trust
- legal or compliance review
- higher infrastructure cost
- reduced portability
- reduced confidence in long-term planning
For users, it may appear as:
- service disruption
- slower access
- reduced reliability
- failed application access
- delayed customer onboarding
- email delivery issues
- platform instability
Most users never see the governance layer.
They only see whether the service works.
That is why governance must be careful when it touches running systems.
A policy debate may look abstract in a meeting room. But for an operator, the same issue may affect customers, contracts, uptime, and business continuity.
The meeting ends.
The network still has to run.
What Responsible Stewardship Should Prioritize
Responsible Internet resource stewardship should prioritize the network before the ritual.
That means governance systems should focus on:
Operational continuity
The first priority should be keeping legitimate, running networks stable wherever possible.
Evidence-based action
Actions affecting live resources should be supported by clear evidence, clear scope, and clear reasoning.
Proportionality
The response should match the problem. Heavy intervention should not be used where a narrow correction would protect the same interest.
Transparency
Operators should understand the process, requirements, consequences, and available remedies.
Accountability
Authority over high-consequence infrastructure should be matched by responsibility for downstream effects.
Portability
Resources should be able to move through clear, lawful, and operationally stable processes.
Technical realism
Rules should reflect how networks actually operate, route, deploy, and depend on number resources.
Separation of coordination and politics
The uniqueness layer should remain as thin, neutral, and operationally focused as possible.
This last point is especially important. The Heng.lu doctrine on “Double Extraction” argues that global uniqueness requires narrow coordination, not thick governance or discretionary institutional gatekeeping.
Larus.Foundation can carry this idea in a compliance-safe way:
A governance layer should be strong enough to preserve uniqueness, but restrained enough not to become a source of avoidable operational risk.
How Larus.Foundation Frames the Issue
Larus.Foundation frames Running-Code Betrayal as a warning about governance design.
The point is not to reject policy.
Policy is necessary.
The point is not to reject coordination.
Coordination is necessary.
The point is not to deny that disputes, reviews, or corrective processes may sometimes be required.
They may be required.
The point is that any system governing Internet number resources must remain subordinate to the operational reality of the Internet.
Live networks are not theoretical objects.
They are the reason the governance layer exists.
For Larus.Foundation, responsible stewardship means asking whether a governance action:
- protects or weakens operational continuity
- clarifies or confuses resource status
- reduces or increases unnecessary risk
- respects or ignores running infrastructure
- supports or undermines operator trust
- keeps coordination narrow or expands it into avoidable control
This is a practical, not ideological, standard.
A trustworthy system should be able to answer these questions clearly.
Final Thought
The Internet was not built by process alone.
It was built by working systems.
Protocols worked.
Networks connected.
Routes converged.
Services reached users.
Operators solved real problems.
Process became valuable because it helped that reality scale.
That order matters.
When process protects running infrastructure, it earns legitimacy.
When process endangers running infrastructure, it loses legitimacy.
That is the heart of Running-Code Betrayal.
For Internet number resource stewardship, the lesson is simple:
The record should serve the network.
The policy should serve continuity.
The coordination layer should serve interoperability.
The governance model should serve the infrastructure people actually use.
If that order is reversed, the Internet does not immediately collapse.
But trust begins to weaken.
And once trust weakens, operators begin looking for clearer, more accountable, more continuity-focused structures.
The future of Internet resource governance should therefore be judged by one practical test:
Does it protect the running Internet?
If the answer is no, then the process may be formal, but it is not sustainable.
Also Read: What Happens When You Lose Control of Your IP Resources?
Frequently Asked Questions
What is Running-Code Betrayal?
Running-Code Betrayal is the moment when governance process, policy interpretation, or administrative procedure begins to endanger infrastructure that is already running. It describes a reversal of the Internet principle that operational reality should discipline governance.
Why does running infrastructure matter in Internet governance?
Running infrastructure matters because users, businesses, applications, and services already depend on it. Governance decisions affecting live networks can create downtime, transfer uncertainty, routing problems, customer disruption, and business-continuity risk.
Does Running-Code Betrayal mean policy is unnecessary?
No. Policy and coordination are necessary. The issue is whether policy remains aligned with operational continuity. A policy process should protect the network, not become detached from the network it is meant to support.
How can Internet resource governance avoid Running-Code Betrayal?
It can avoid Running-Code Betrayal by prioritizing operational continuity, evidence-based decisions, proportionality, transparency, accountability, portability, and technical realism.
Why is this relevant to IPv4 and Internet number resources?
IPv4 addresses, IPv6 addresses, ASNs, routing records, and registry records are embedded in real infrastructure. When governance touches these resources, it can affect hosting, cloud, telecom, VPN, security, email, enterprise access, and customer-facing services.